Our Innovation Story – In Video
Watch now Flow’s 3-minute story
For those who prefer the written word, here’s our story
In ancient times, each village’s primary source of water was also its source of life. Therefore it was crucial to place a guard on that one water source to protect it against malicious theft or sabotage.
But with time as villages got bigger, protecting water got more challenging. Water started to be widely distributed, stored in various places, and traded with other villages. Water protection became an impossible task.
This is exactly what happens today when companies try to protect their source of life – sensitive data. Sensitive data, just like water, is highly fragmented and flows everywhere in an ever-changing environment. It is prone to be leaked, ransomed, or stolen; causing colossal damage.
Data liquidity requires a new approach to data security. Flow Security offers a data security platform that revolutionizes how security teams protect their data.
Flow’s DSPM solves companies’ biggest data security challenges:
- Data discovery
- Data classification
- Automated data flow mapping
- Data risk management
- Real-time data detection and response
How do we do it? This is what makes our solution unique.
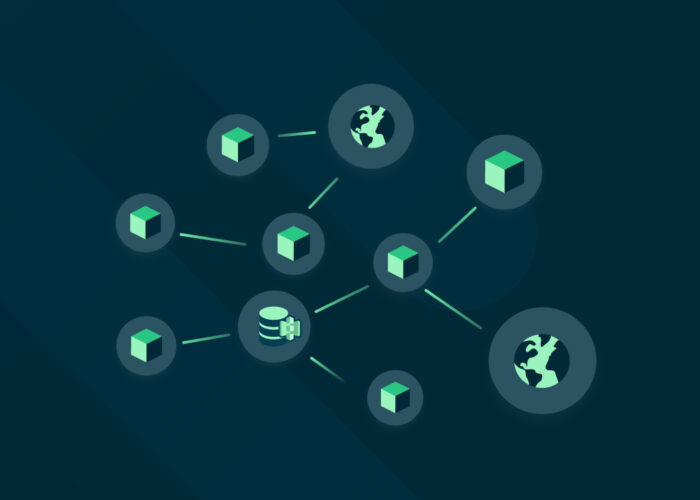
Our platform scans and classifies data stores at rest, but it doesn’t stop there. It goes forward by analyzing data in motion as well. By leveraging the eBPF technology and, using a one-click deployment, our platform has the ability to analyze data payloads as they flow within and outside the environment. By tracking and mapping all data flows, our platform has the “all-seeing-eye capability” that covers data in the darkest corners of the environment and provides a deep understanding of its applicative context.
Let’s see an example based on hundreds of incidents our customers find on a weekly basis.
We got a message alerting me of a sensitive data leakage incident. A new sensitive data flow was detected from a service called “Analytics” to Salesforce.

But why? Where is this data coming from? Who is in charge of this?
With Flow I can see the full picture. By following the data flows, I understand that the origin of the data leakage is an unusual database. It looks like an unmanaged, misconfigured and risky asset. I can easily analyze it and take action to solve it directly with the asset owner. Without data flow analysis, none of this could have been done, making Flow the only solution to solve these impossible challenges.
Flow defines the DSPM category by being the first and only vendor to combine data-at-rest with data-in-motion analysis.
Flow was founded in early 2021 and is led by top notch security and industry experts. We have the honor of working with amazing organizations, including Fortune 500 companies, as our customers.